
Over the past month, our efforts have focused on advancing Inheriti® Elements from structured B2B integration into validated production environments, where performance, resilience, and architectural efficiency can be measured under real-world conditions. As Inheriti® Elements increasingly operates as an embedded trust layer within partner ecosystems, we continue refining deployment standards, optimizing system robustness, and strengthening enterprise readiness. In parallel, all public VeChain Network clusters—both testnet and mainnet—have been successfully upgraded to Thor version 2.4.2, reinforcing network stability, scalability, and long-term reliability. Together, these milestones reflect steady progress toward delivering secure, compliant, and future-ready digital trust infrastructure at scale.
Structured B2B Implementation & Integration
Following the release of the SDK, our focus has shifted toward structured implementation with selected B2B partners across multiple environments. Inheriti® Elements is being integrated as a core security component within existing platforms, supporting use cases such as encrypted data protection, dynamic access governance, robust key recovery, and identity-based trust frameworks. Through close collaboration with partner development teams, we ensure architectural compatibility, regulatory alignment, and operational stability from day one. These deployments allow us to continuously enhance integration methodologies, mature documentation standards, and further solidify Inheriti® Elements as a scalable, enterprise-ready trust infrastructure.
In parallel, we are formalizing standardized deployment blueprints to streamline future integrations. By documenting configuration models, integration flows, and architectural best practices, we are reducing implementation complexity while preserving the integrity of our zero-trust design principles. This structured approach ensures that future partners can adopt Inheriti® Elements efficiently without compromising security depth or operational continuity.

Production Validation & Performance Optimization
As integrations advance, we are now observing how Inheriti® Elements performs under live production conditions, including transaction throughput, recovery execution flows, and system-level resilience. This stage is critical—not only for performance benchmarking, but for stress-testing edge cases that cannot be replicated in isolated development environments. Insights gathered from these deployments directly inform architectural optimizations, SDK refinements, and expanded configuration flexibility.
Beyond performance metrics, this phase provides valuable visibility into real-world usage behavior and workflow interaction patterns. These insights allow us to fine-tune resource allocation, optimize cryptographic execution efficiency, and further strengthen system robustness. Each iteration enhances both technical precision and deployment confidence, reinforcing the long-term reliability of the framework.

Aligning Cryptographic Trust with Enterprise Governance
As enterprise integrations progress, we continue to strengthen Inheriti® Elements’ alignment with strict compliance and regulatory requirements across diverse jurisdictions. The framework’s zero-trust design philosophy ensures that access is cryptographically enforced rather than assumed, reducing systemic risk while supporting auditability and governance standards expected by enterprise environments. By leveraging a non-custodial architecture, Inheriti® Elements eliminates centralized key control, mitigating counterparty exposure and enhancing operational transparency. This structure also reinforces data sovereignty principles, allowing organizations to maintain control over sensitive information while integrating advanced cryptographic protection within their existing compliance frameworks.

Building Long Term Foundational Trust Infrastructure
Looking ahead, our long-term vision extends beyond positioning Inheriti® Elements as a standalone product—we are deliberately building toward foundational infrastructure status. The objective is to make embedded cryptographic trust a baseline standard within digital systems, rather than an optional security enhancement layered on top. By integrating non-custodial, zero-trust principles directly into core architecture, we are aligning Inheriti® Elements with the structural needs of modern enterprise ecosystems. As the framework continues to mature, our roadmap remains focused on expanding infrastructure capabilities, strengthening interoperability, and enabling scalable adoption—advancing toward a future where cryptographic trust is seamlessly embedded across digital environments.

Try Inheriti® Today — Protect Your Digital Legacy for Free
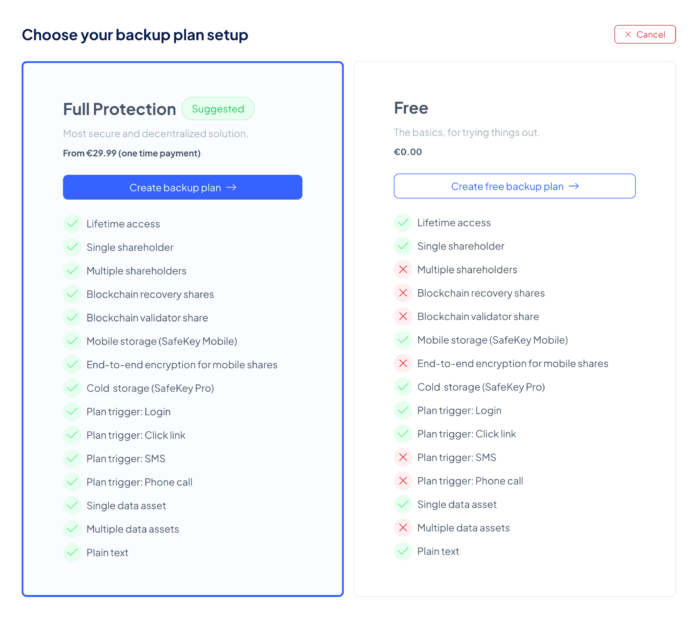
Your digital legacy deserves protection — and getting started should be simple. With Free Backup Plans in Inheriti®, anyone can take their first step into digital inheritance at no cost. A Free Plan allows you to create a basic backup, assign a single shareholder for personal use, and securely store your encrypted information using SafeKey Mobile. Whether it’s passwords, PIN codes, private keys, or plain text, you can safeguard what matters most in just a few clicks.
Free Backup Plans are designed to let you explore Inheriti® firsthand. They provide a practical introduction to the platform’s core features — from generating encrypted shares to protecting your digital assets securely.
The main difference lies in how the validator share is stored. With paid plans, it is recorded on the blockchain of your choice, while Free Plans keep it safe in the Inheriti® Vault. Both methods ensure your data is fully protected, but Free Plans simplify onboarding by removing blockchain dependencies, making Inheriti® more accessible to everyone.
How to Get Started:
- Go to app.inheriti.com
- Create your SafeID account
- Log in to the platform
- Select Create New Backup Plan
- Choose Free Plan
By introducing Free Backup Plans, our objective is clear: to make digital inheritance accessible to everyone, reduce barriers to entry, and provide a straightforward way to protect sensitive information with confidence.
We encourage you to create your own Free Backup Plan today and experience firsthand how simple and secure it is to safeguard your digital legacy with Inheriti®. It’s an ideal starting point — safe, seamless, and without risk.
Vechain Nodes Upgrade
All public VeChain Network clusters, including both testnet and mainnet, have been successfully upgraded to the latest Thor version 2.4.2. We’re pleased to confirm that all public VeChain network nodes are operating smoothly, delivering improved performance, enhanced reliability, and greater network stability. These upgrades are essential to maintaining VeChain’s high blockchain standards, ensuring seamless transactions and increased scalability as the ecosystem continues to expand. This milestone reinforces our ongoing focus on strengthening the network’s foundation to support long-term growth, innovation, and enterprise adoption.
All Public #VechainNetwork (test and mainnet clusters) are upgraded to the latest #Thor version 2.4.2 @vechainofficial @SafeTech_Labs https://t.co/LbWggbNGXa pic.twitter.com/7yrU0O0065
— Jûrgen Schouppe founder @Inheriti.com (@jurgenschouppe) February 15, 2026
Community
Strong month. SDK, B2B partnerships, and staking updates show both infrastructure growth and ecosystem engagement. Execution on developer tools and platform trust will drive adoption. @SafeHavenio follow back appreciated fr
— PunkXBT (@PunkXBT_) February 2, 2026
Back to newsThinking @SafeHavenio is a rough diamond for 2 years already. The team is still working and providing monthly updates. Time to start accumulating. Posting this for myself. Would be funny to look back at this post when #safehavenio takes off. pic.twitter.com/EDTQUc8yLQ
— Makudonarudo (@MakudonarudoVET) February 27, 2026

 Nederlands
Nederlands Deutsch
Deutsch Français
Français