
Deepening Integration Across Systems
Throughout the month, integrations have naturally moved beyond initial implementation into deeper and more complex environments. Partners are no longer just embedding individual components, but are beginning to integrate full trust flows into their applications. This includes multi-step access control across user journeys, secure handling of sensitive data within application logic, more advanced key recovery processes tied to identity conditions, and distributed control models across multiple stakeholders. It’s a clear step forward from feature-level integration toward something that becomes part of the system itself.

From Deployment Blueprints to Repeatable Models
The deployment frameworks introduced in February have now been put into practice and refined through real use. As partners begin integrating Inheriti® Elements into their own systems, these initial blueprints are being tested across different environments, use cases, and technical setups. This process is helping identify where integrations can be simplified, where flexibility is needed, and how to reduce friction for development teams working with the SDK.
Over time, these blueprints are evolving into repeatable deployment models that make integrations smoother and more predictable for new partners. Instead of starting from scratch, teams can rely on proven integration patterns that have already been validated in real-world conditions. This not only shortens implementation timelines but also increases confidence in how the system behaves once deployed.
A key part of this effort has been standardizing how the SDK is implemented across different environments, whether in cloud-based systems, client-side applications, or hybrid architectures. Alongside this, clearer configuration models are being defined to support a range of use cases, from simple recovery flows to more advanced multi-party access scenarios. Developer onboarding is also being improved, with more structured guidance that helps teams move from initial setup to full integration more efficiently.
The broader goal behind this work is to remove complexity wherever possible. Advanced cryptographic security often comes with a high barrier to entry, but by refining these deployment models and making integrations more intuitive, Inheriti® Elements is becoming easier to adopt without compromising on security. Over time, this approach supports a more scalable rollout, where new integrations can be implemented faster, with less overhead, and with greater consistency across different partners and systems.

Performance Optimization and System Maturity
Throughout March, continued execution across live integrations has provided clearer insight into how Inheriti® Elements performs under real-world conditions. As usage increases, performance is being evaluated not in isolation, but as part of broader application flows where reliability and consistency are critical.
A key focus has been improving throughput and ensuring the system can handle sustained activity without degradation. This includes optimizing how operations are processed and distributed, allowing the system to respond more efficiently under varying load conditions.
At the same time, attention has been given to the stability of recovery execution processes. These flows are among the most sensitive parts of the system, and ongoing testing has helped improve consistency and reduce edge cases across different environments.
Efforts have also been directed toward strengthening resilience across distributed and hybrid infrastructures, ensuring stable behavior across cloud, client-side, and offline components. These improvements are driven directly by real-world usage and partner feedback, allowing Inheriti® Elements to mature in a practical and reliable way as adoption continues to grow.

VeChain Network Updated to Thor 2.4.3
All public VeChain Network clusters, including both testnet and mainnet environments, have been successfully upgraded to the latest Thor version 2.4.3. This upgrade ensures improved network performance, enhanced stability, and continued alignment with the latest protocol developments. Keeping all clusters up to date is essential for maintaining reliability across the ecosystem, supporting ongoing integrations, and providing a solid foundation for future development and scalability.
All Public #VechainNetwork (test and mainnet clusters) are upgraded to the latest #Thor version 2.4.3 @vechainofficial @SafeTech_Labs https://t.co/LbWggbN97C pic.twitter.com/S5OVg7irly
— Jûrgen Schouppe founder @Inheriti.com (@jurgenschouppe) March 29, 2026
Try Inheriti® Today — Protect Your Digital Legacy for Free
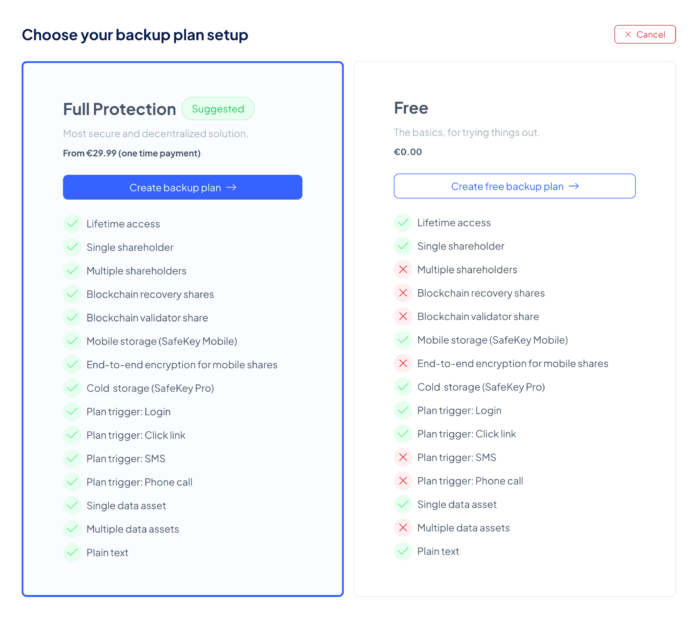
Your digital legacy deserves protection — and getting started should be simple. With Free Backup Plans in Inheriti®, anyone can take their first step into digital inheritance at no cost. A Free Plan allows you to create a basic backup, assign a single shareholder for personal use, and securely store your encrypted information using SafeKey Mobile. Whether it’s passwords, PIN codes, private keys, or plain text, you can safeguard what matters most in just a few clicks.
Free Backup Plans are designed to let you explore Inheriti® firsthand. They provide a practical introduction to the platform’s core features — from generating encrypted shares to protecting your digital assets securely.
The main difference lies in how the validator share is stored. With paid plans, it is recorded on the blockchain of your choice, while Free Plans keep it safe in the Inheriti® Vault. Both methods ensure your data is fully protected, but Free Plans simplify onboarding by removing blockchain dependencies, making Inheriti® more accessible to everyone.
How to Get Started:
- Go to app.inheriti.com
- Create your SafeID account
- Log in to the platform
- Select Create New Backup Plan
- Choose Free Plan
By introducing Free Backup Plans, our objective is clear: to make digital inheritance accessible to everyone, reduce barriers to entry, and provide a straightforward way to protect sensitive information with confidence.
We encourage you to create your own Free Backup Plan today and experience firsthand how simple and secure it is to safeguard your digital legacy with Inheriti®. It’s an ideal starting point — safe, seamless, and without risk.
Harness the Power of SafeSwap: A Complete Guide to Building Your Own Atomic Swap Platform
This marks an important milestone for our SafeSwap product, showcasing a major advancement in providing developers and businesses with fast, secure, and scalable cross-chain token swap solutions. Launch your own atomic swap platform in days instead of months with our robust white-label solution. Built to empower both businesses and developers, this platform enables seamless native token swaps across multiple blockchains, fully integrated through a comprehensive API. Engineered for speed, scalability, and security, our solution guarantees smooth and reliable transactions, even under high user demand. Whether you’re entering the decentralized exchange market or enhancing your existing services, our white-label platform offers a fast, secure, and customizable way to deliver state-of-the-art cross-chain swap capabilities to your users.

This link (https://docs.safeswap.io/builders/api-integration-guide) will guide you through integrating your dApp with SafeSwap. Your front end will interact directly with the SafeSwap smart contract and our API to facilitate seamless token swaps. Inside, you’ll find detailed information covering:
- Prerequisites
- What is a Swap?
- How to Perform a Swap
- Smart Contract Details
- Our Swap Addresses
- API Specifications
Consult this guide to gain detailed insights and smoothly integrate your application, unlocking the full power of SafeSwap’s decentralized swapping technology.
Security Notice: Scam Warning and Community Reminder
We want to make the community aware of ongoing scam attempts involving individuals impersonating members of our team and sending direct messages. There is currently no new token, no V2 launch, and no token swap taking place—any message claiming otherwise is false and should be treated as a scam. As a reminder, we will never initiate contact through direct messages, and we will never ask for your wallet details, private keys, or sensitive information. Please avoid clicking on any suspicious links and always verify information through our official channels. If you receive such messages, ignore them and report them immediately. Staying cautious and informed is the best way to protect yourself and others in the community.
Community
Yesterday and just now! Your right everyone needs a solution to their inevitable passing. Here today gone tomorrow it's not fun to think about but its reality.
Everyone should take the 🏋♀️🏋♂️ of inheritance of their shoulders with @Inheriti_com @SafeHavenio #VebetterDAO
— VEcosystemT (@Vecosystem_t) March 2, 2026
I'm still holding my SHA node. No reason to let it go at these prices. The team is still around and doing things. I think I forgot to stake this month though.
— waixingren (@Waixingren) March 21, 2026
$SHA, up only since Nov, 2024, like wtf, and people are like why you so dang bullish on vechain.
Mfkrs, look at the chart, nobody buying the last two years is down. . . You keep your solana. pic.twitter.com/mNukD130X2
— Gnomie (@CryptoGnomie) March 28, 2026
Back to news

 Nederlands
Nederlands Deutsch
Deutsch Français
Français